In complex software architecture, managing how components interact is as critical as the code itself. Package visibility defines the boundaries of access between different modules within a system. When you construct a package diagram, you are not merely drawing boxes; you are defining the contract of interaction between teams, layers, and subsystems. Understanding the rules of package visibility ensures that your system remains maintainable, secure, and scalable over time.
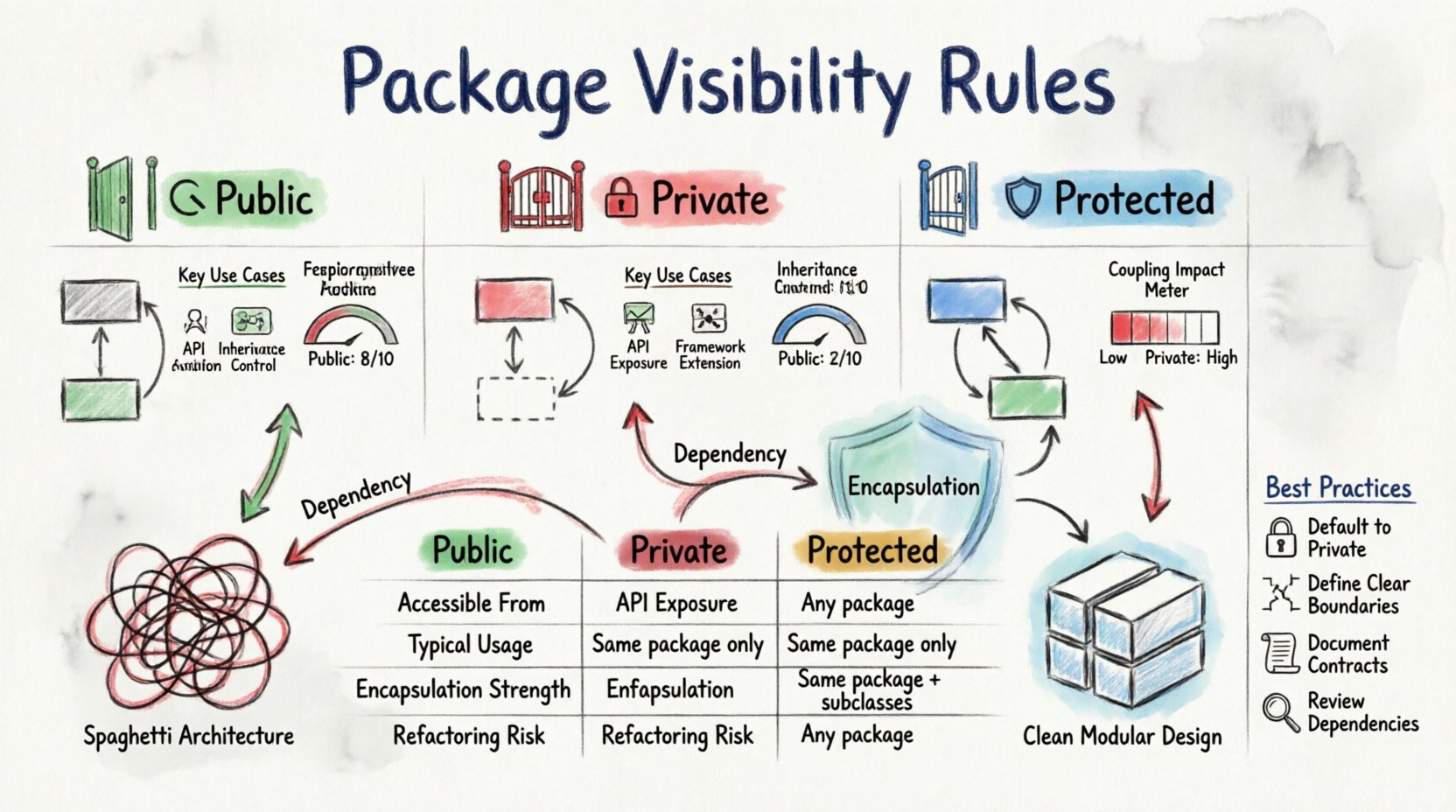
This guide explores the three primary states of visibility: Private, Public, and Protected. We will examine how each rule affects coupling, cohesion, and the overall health of the architecture. Whether you are designing a monolithic application or a distributed microservices ecosystem, these principles apply universally to model-driven development and software design.
🏗️ Understanding the Concept of Package Visibility
A package represents a logical grouping of related elements. It could be a set of classes, interfaces, or subsystems that function together to solve a specific domain problem. However, without visibility rules, every package could access every other package, leading to a tangled web of dependencies known as a spaghetti architecture.
Visibility acts as a gatekeeper. It determines who can see what. This is not just about hiding implementation details; it is about controlling the surface area of your system. When visibility is too open, changes in one area can inadvertently break another. When visibility is too closed, the system becomes rigid and difficult to integrate.
Key considerations for visibility include:
- Encapsulation: Keeping internal logic hidden from external consumers.
- Decoupling: Reducing dependencies between unrelated modules.
- Discoverability: Ensuring that public interfaces are clear and accessible where needed.
- Security: Preventing unauthorized access to sensitive data or logic.
🔓 Public Visibility: The Open Door
Public visibility is the most permissive state. Elements marked as public are accessible from any other package within the system. This is the standard interface through which external modules interact with your package.
When to Use Public Visibility
Public visibility should be reserved for stable, well-defined APIs. It is the contract you offer to the rest of the system. If a package exposes too many public elements, it becomes a leaky abstraction, where internal implementation details escape the boundaries of the module.
- Core Services: If a package provides a fundamental service that many other packages rely on, its primary interfaces should be public.
- Entry Points: The initial access points for a subsystem should be public to allow integration.
- Domain Models: Entities that represent business concepts often need to be public so that different layers can manipulate them.
Implications of Public Visibility
While public visibility facilitates integration, it comes with significant responsibilities. Every public element is a potential point of failure. If you change a public method signature, you break the contract for every consumer of that package. This necessitates rigorous versioning and backward compatibility strategies.
Common risks include:
- High Coupling: Other packages may become dependent on specific internal classes that were intended to be internal.
- Refactoring Difficulty: Changing the internal structure becomes risky because external packages might be relying on the exposed details.
- Security Exposure: Sensitive data structures might be inadvertently exposed if not carefully audited.
🔒 Private Visibility: The Locked Room
Private visibility restricts access to the package itself. No other package can directly access elements marked as private. This is the strongest form of encapsulation. It ensures that the internal workings of a module remain opaque to the rest of the system.
When to Use Private Visibility
Private visibility is the default state for implementation details. It is used for helper methods, temporary variables, and internal algorithms that should not be influenced by external logic.
- Implementation Helpers: Functions that support the public API but are not useful or understandable outside the package.
- State Management: Internal state variables that should only be modified through public methods.
- Third-Party Wrappers: If you are wrapping an external library, keep the internal adapter logic private.
Benefits of Private Visibility
Using private visibility liberates the developer. You can change the implementation of a private element without affecting anyone else. This encourages agility and allows for continuous improvement without fear of breaking external dependencies.
Key advantages include:
- Stability: The public contract remains stable even if the internal code changes drastically.
- Clarity: Consumers of the package do not need to understand how the package works, only what it does.
- Control: You maintain full control over how the package behaves internally.
🛡️ Protected Visibility: The Semi-Open Gate
Protected visibility sits between public and private. It allows access from the package itself and from packages that are considered part of the same subsystem or family. This is often used in hierarchical architectures where a parent package defines rules that child packages follow.
When to Use Protected Visibility
Protected visibility is ideal for extension points. It allows you to share logic with trusted sub-modules without exposing that logic to the entire system.
- Sub-packages: If a package contains sub-packages, protected visibility allows them to share internal utilities.
- Plugin Systems: If you have a plugin architecture, protected visibility can allow plugins to access core mechanisms without making them public.
- Inheritance Patterns: In some modeling contexts, protected visibility mimics inheritance behavior where derived classes can access base class internals.
Considerations for Protected Visibility
Protected visibility requires clear definitions of what constitutes a “family” or “subsystem.” Ambiguity here can lead to confusion about who has access to what. It is crucial to document the hierarchy clearly so that developers understand the scope of protected elements.
Potential challenges include:
- Scope Confusion: Developers may assume protected elements are private, or vice versa.
- Indirect Coupling: Sub-packages may become tightly coupled to the parent package’s internal structure.
- Testing Complexity: Testing protected elements often requires specific access setups that public elements do not.
📊 Comparison of Visibility Rules
Understanding the differences is easier when viewed side-by-side. The table below summarizes the access levels, typical use cases, and impact on the system.
| Visibility Level | Access Scope | Primary Use Case | Impact on Coupling |
|---|---|---|---|
| Public 🔓 | Any package in the system | Stable APIs, Entry Points | Increases risk of high coupling |
| Private 🔒 | Package itself only | Implementation Details, Helpers | Reduces coupling, increases encapsulation |
| Protected 🛡️ | Package and Sub-packages | Extension Points, Internal Sharing | Balanced coupling within hierarchy |
🛠️ Best Practices for Implementation
Applying visibility rules correctly requires discipline. It is not enough to know the definitions; you must apply them consistently throughout the design and development lifecycle.
1. Default to Private
Adopt a mindset where visibility is restrictive by default. Only expose what is absolutely necessary. This minimizes the surface area of your system and reduces the likelihood of accidental dependencies.
2. Define Clear Boundaries
Ensure that package boundaries align with logical domain boundaries. If a package contains two distinct concepts, split them. This makes visibility rules more meaningful and easier to manage.
3. Document the Contract
For public elements, documentation is mandatory. Consumers need to know how to use the interface. For protected elements, internal documentation should explain the hierarchy and usage rules.
4. Review Dependencies
Regularly audit the dependency graph. Look for packages that depend on internal classes of other packages. This often indicates a visibility violation that should be corrected.
⚠️ Common Pitfalls to Avoid
Even experienced architects can make mistakes with visibility. Recognizing these pitfalls early can save significant technical debt.
- Over-Exposing Interfaces: Creating a public API that is too granular. It is better to group functionality into cohesive units rather than exposing every small function.
- Ignoring Protected Nuances: Assuming protected access works the same way across all modeling contexts. Some environments treat protected differently than others.
- Static Access: Using static methods that bypass visibility rules can lead to hidden dependencies that are hard to trace.
- Circular Dependencies: Visibility rules do not prevent circular dependencies. Two packages can be public to each other but still create a cycle that breaks compilation or execution.
🔄 Impact on Maintenance and Scalability
The choice of visibility rules directly influences how easily a system can be maintained and scaled. A well-structured visibility model allows teams to work in parallel without stepping on each other’s toes.
Maintenance
When visibility is well-managed, refactoring becomes a localized task. You can change the internals of a package without worrying about breaking the rest of the system. This reduces the cost of change and increases the velocity of development.
Scalability
As the system grows, the number of packages increases. Without strict visibility rules, the complexity of interactions grows exponentially. By limiting access, you control the complexity curve. This makes it easier to onboard new developers, as the public interface serves as the primary source of truth.
Team Structure Alignment
Visibility rules can mirror team boundaries. If you have a team responsible for a specific package, that package should expose only what that team wants others to use. This aligns technical architecture with organizational structure, a concept often referred to as Conway’s Law.
🚀 Strategies for Migration and Refactoring
Existing systems often have poor visibility structures. Moving from a loose structure to a strict one requires a plan.
Phase 1: Audit
Map out all current dependencies. Identify which packages are exposing too much and which are under-utilizing public interfaces.
Phase 2: Stabilize
Ensure that the public interfaces are stable. Do not refactor the public API while simultaneously changing visibility rules. Fix the contract first.
Phase 3: Restrict
Gradually move implementation details to private. Introduce protected visibility for shared utilities before removing public access.
Phase 4: Verify
Run comprehensive tests to ensure that the system still functions correctly after visibility changes. Automated testing is essential for this phase.
🔗 The Relationship Between Visibility and Dependencies
Visibility and dependency are closely linked. Visibility defines what can be accessed, while dependency defines what is accessed. A healthy system minimizes dependencies by maximizing visibility restrictions.
When a package depends on another, it should depend on the public interface. If it depends on internal classes, it creates a fragile link. This is often called internal dependency. Ideally, internal dependencies should be eliminated or minimized.
Consider the following dependency patterns:
- Direct Dependency: Package A uses Package B’s public API. This is the desired pattern.
- Internal Dependency: Package A uses Package B’s private or protected classes. This should be avoided unless Package A is a sub-package.
- Implicit Dependency: Package A relies on Package B’s side effects. This is dangerous and should be eliminated.
🌐 Visibility in Distributed Systems
In distributed architectures, visibility rules extend beyond the codebase. They apply to network boundaries and API gateways. A package might be public within a service but private in the context of the broader system.
This requires a layered approach:
- Service Boundary: Define which services are public-facing and which are internal-only.
- API Gateway: Use the gateway to enforce visibility rules at the network level.
- Data Contracts: Ensure that data models exposed publicly are versioned and stable.
📝 Summary of Key Takeaways
Managing package visibility is a foundational skill in software architecture. It requires a balance between openness for integration and restriction for safety. By adhering to the principles of private, public, and protected visibility, you create systems that are robust and adaptable.
Remember the core principles:
- Keep implementation details private.
- Make only necessary interfaces public.
- Use protected visibility for internal hierarchy sharing.
- Audit dependencies regularly.
- Align visibility with team boundaries.
By applying these rules consistently, you build a foundation that supports long-term growth and stability. The effort invested in defining visibility early pays dividends in reduced maintenance costs and increased development speed over the life of the project.











