Software systems rarely start as legacy code. They begin with intention, structure, and a clear vision for the future. However, over time, requirements shift, teams change, and business pressures mount. The result is often a system that works but does not feel right. It is brittle, difficult to understand, and resistant to change. This is the reality of legacy code.
When facing such a system, the instinct might be to rewrite it entirely. Yet, rewriting is often riskier than maintaining. The solution lies not in abandonment, but in transformation. Object-Oriented Analysis and Design (OOAD) provides a robust framework for understanding, refactoring, and improving these systems without discarding the value they already hold.
This guide explores how to apply Object-Oriented principles to legacy codebases. We will move beyond theory and look at practical strategies for identifying objects, managing dependencies, and introducing structure where there is currently chaos. The goal is not to make the code beautiful for aesthetics, but to make it maintainable for the humans who must work with it tomorrow.
🧱 Understanding the Nature of Legacy Code
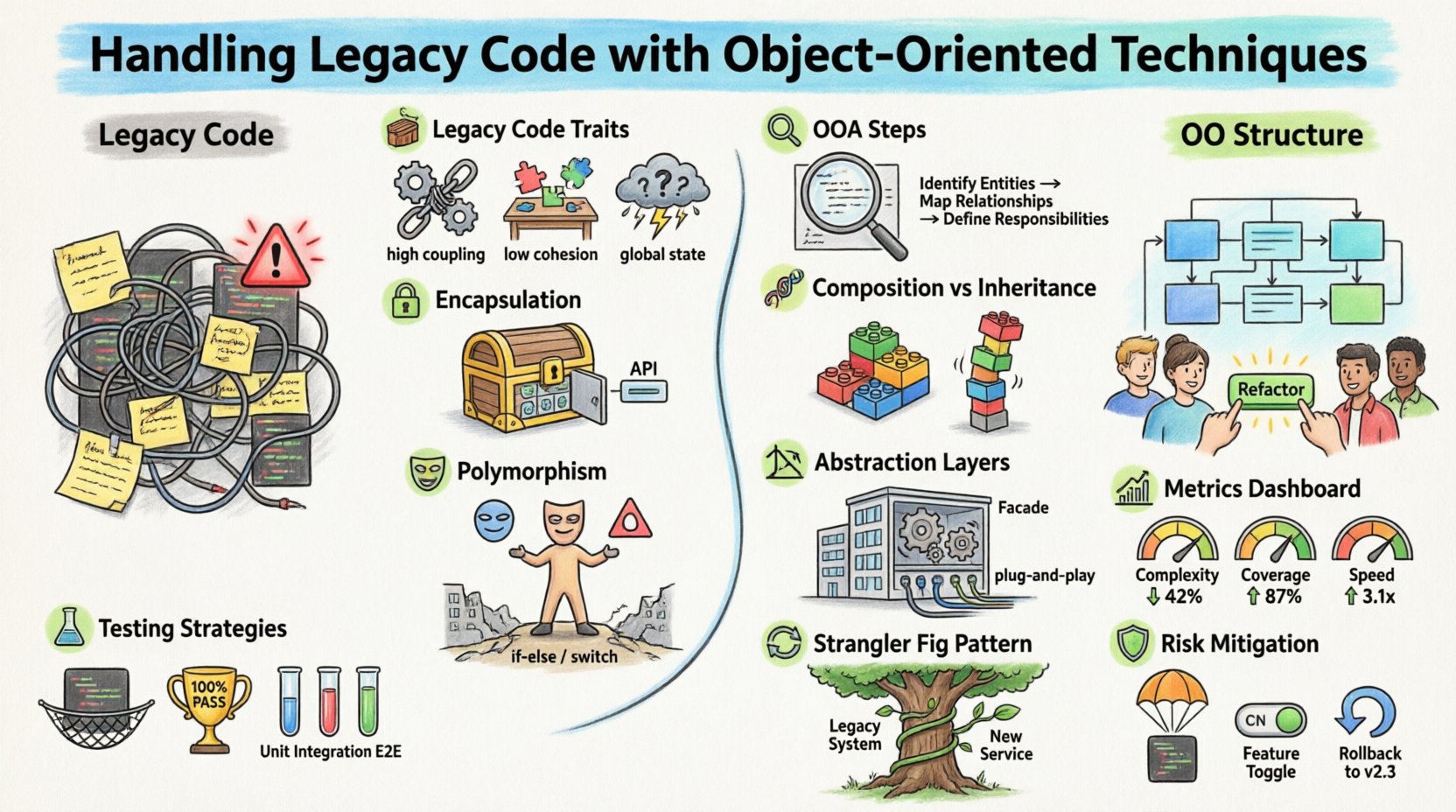
Legacy code is not simply old code. It is code that lacks sufficient automated tests to support changes. It is often written in a style that predates modern design patterns. In many cases, legacy systems were built using procedural paradigms, where functions and global state dominate the architecture.
Transitioning from procedural to object-oriented thinking requires a shift in perspective. Instead of focusing on the sequence of operations, you must focus on the interactions between entities. These entities are the objects.
Key Characteristics of Legacy Systems
- High Coupling: Components are tightly dependent on one another, making isolated changes difficult.
- Low Cohesion: Classes or functions perform unrelated tasks, leading to confusion.
- Hidden Dependencies: Logic is buried deep within the call stack, making it hard to trace data flow.
- Global State: Shared variables across the system create unpredictable behavior during concurrent operations.
- Lack of Documentation: The code itself is the only source of truth, and it is often outdated.
🔍 Object-Oriented Analysis for Legacy Systems
Before refactoring a single line of code, you must analyze the existing system. Object-Oriented Analysis (OOA) is the process of defining the problem domain and identifying the objects that will solve it. In a legacy context, this means reverse-engineering the behavior to find the logical objects hidden within the procedural mess.
Step 1: Identify Responsibilities
Look for distinct areas of responsibility within the codebase. Even in a procedural script, there are often distinct functional areas. For example, a function that handles database connections has a different responsibility than a function that formats reports.
- Identify Data Structures: Where is data stored? Is it scattered in global variables or grouped in structures?
- Identify Behaviors: What operations are performed on this data? Are they repetitive?
- Group by Domain: Assign data and behavior to logical groups based on business concepts.
Step 2: Map Entities to Objects
Once responsibilities are identified, map them to object-oriented concepts. This is the bridge between the old system and the new design.
- Entities: These represent the core concepts of the business, such as Customer, Order, or Product.
- Value Objects: These are immutable objects that describe a specific attribute, such as Address or Money.
- Services: These handle operations that do not belong to a specific entity, like NotificationService.
🔒 Applying Encapsulation Principles
Encapsulation is the practice of hiding internal state and requiring all interaction to occur through a well-defined interface. In legacy code, global variables and public access to internal data are common. This leads to side effects that are hard to predict.
Breaking Open Classes
Legacy classes often expose every variable as public. To fix this:
- Make Fields Private: Restrict access to data members within the class.
- Expose Properties: Provide getters and setters that validate data before assignment.
- Enforce Invariants: Ensure that the object is always in a valid state upon creation and modification.
Controlling Access
Not all data needs to be visible everywhere. Use access modifiers to control visibility. If a method is internal to the class logic, mark it as private. If it is part of the public contract, mark it as public.
| Legacy Pattern | OO Encapsulation Pattern | Benefit |
|---|---|---|
| Global Variables | Private Fields | Prevents unintended external modification |
| Public Methods for Everything | Interface-Based Access | Reduces coupling between modules |
| Direct Database Access in Business Logic | Repository Pattern | Decouples logic from data storage |
🧬 Managing Inheritance and Composition
Inheritance allows a class to derive properties and behaviors from another class. While useful, legacy code often suffers from deep and complex inheritance hierarchies that are hard to navigate. This is often referred to as the “Fragile Base Class Problem.”
Composition Over Inheritance
A safer approach in modern design is composition. Instead of inheriting behavior, an object holds references to other objects that provide that behavior.
- Flexible Behavior: You can change the behavior at runtime by swapping the composed object.
- Clearer Boundaries: The relationship is explicit in the class definition.
- Reduced Coupling: Changes in the base class do not ripple through the hierarchy as aggressively.
Refactoring Inheritance Chains
If you encounter a long chain of inheritance:
- Extract Superclass: Identify commonalities and pull them into a new base class.
- Replace Inheritance: Move the logic to a separate service and inject it.
- Use Mixins: If supported by the language, use mixins for specific behaviors without full inheritance.
🎭 Leveraging Polymorphism
Polymorphism allows objects to be treated as instances of their parent class rather than their actual class. This enables code to handle different types of objects uniformly. Legacy code often uses conditional logic (if-else or switch statements) to handle different types, which violates the Open/Closed Principle.
Eliminating Conditional Logic
Look for long switch statements that check object types. These are signals that polymorphism is missing.
- Create Base Classes: Define a common interface for the different types.
- Implement Specific Behavior: Let each subclass implement the method it needs.
- Use a Factory: Create an object that returns the correct instance based on input, keeping the caller unaware of the specific type.
Interface Segregation
Ensure that your interfaces are specific. A legacy interface that requires every class to implement methods it doesn’t need should be split. This reduces the burden on implementers and makes the code easier to test.
🏗️ Building Abstraction Layers
Abstraction hides complex implementation details and exposes only the necessary parts. In legacy systems, business logic is often mixed with infrastructure code (database calls, file I/O, network requests).
Introducing Facades
A Facade provides a simplified interface to a complex subsystem. You can wrap legacy logic in a facade to present a clean API to the rest of the system.
- Decouple Entry Points: New code interacts with the facade, not the legacy logic.
- Gradual Replacement: You can replace the underlying implementation of the facade over time without breaking callers.
Dependency Injection
Hard-coded dependencies make testing and replacement difficult. Introduce dependency injection to allow objects to receive their dependencies from the outside.
- Constructor Injection: Pass dependencies when creating an object.
- Setter Injection: Set dependencies after creation (use sparingly).
- Interface Injection: The dependency defines the injection mechanism.
🧪 Testing Strategies for Refactoring
Refactoring legacy code without tests is dangerous. You need a safety net to ensure behavior remains consistent.
Golden Master Tests
When you cannot modify the code to add tests easily, record the input and output of the system as a “Golden Master.” Run your tests against this record. If the output changes, you know something has broken.
Characterization Tests
Write tests that describe the current behavior, even if that behavior is flawed. These tests capture the “as-is” state. As you refactor, these tests ensure you do not accidentally fix the bug that users rely on.
Unit Testing Refactored Components
Once you have extracted a class or function, write unit tests for it. Isolate the logic from the infrastructure. This allows you to refactor the internal implementation of that unit without worrying about the broader system.
⚠️ Common Pitfalls to Avoid
Refactoring is a delicate process. There are common mistakes that can slow down progress or introduce new bugs.
- Over-Engineering: Do not introduce patterns that are not needed. Keep the design as simple as possible for the current requirements.
- Ignoring Tests: Never refactor without a test plan. If you cannot test it, do not change it.
- Big Bang Refactoring: Do not try to fix the whole system at once. Work in small, incremental steps.
- Ignoring Context: Understand the business domain. Refactoring for the sake of elegance can make the code harder to understand for domain experts.
📊 Measuring Improvement
How do you know if your refactoring is working? You need metrics that reflect code health and maintainability.
| Metric | Goal | Why It Matters |
|---|---|---|
| Cyclomatic Complexity | Lower | Indicates how many paths exist through a function. Lower is easier to test. |
| Code Coverage | Higher | Ensures more of the code is exercised by tests. |
| Test Execution Time | Faster | Indicates better isolation and fewer dependencies. |
| Technical Debt Ratio | Lower | Estimates the cost to fix issues found by static analysis. |
🔄 Strategic Approaches for Migration
Sometimes, OOP principles cannot be applied directly to the existing codebase without massive disruption. In these cases, strategic patterns help bridge the gap.
The Strangler Fig Pattern
This pattern involves gradually replacing legacy functionality with new services. You build a new system alongside the old one and route traffic to the new system piece by piece until the old system is removed.
The Facade Pattern
Create a unified interface that wraps the legacy code. New code calls the facade. Over time, the facade can be replaced with a new implementation, leaving the legacy code behind.
Dependency Injection Containers
Use a container to manage object creation and dependencies. This allows you to swap out legacy implementations with new ones without changing the client code.
🛡️ Risk Mitigation
Every change in a legacy system carries risk. Mitigation involves careful planning and communication.
- Feature Toggles: Use flags to enable new functionality without deploying it to all users.
- Canary Releases: Deploy changes to a small subset of users first.
- Rollback Plans: Have a verified way to revert changes quickly if issues arise.
- Communication: Keep stakeholders informed about progress and potential risks.
🧩 Final Thoughts on Evolution
Refactoring legacy code is not a one-time project. It is a continuous process of improvement. By applying Object-Oriented Analysis and Design principles, you transform the system from a static burden into a dynamic asset.
The key is patience. Do not rush. Focus on small, verifiable improvements. Ensure that every step makes the system safer and easier to understand. Over time, these small changes accumulate into a significant transformation.
Remember that the goal is not perfection. It is progress. A system that is slightly better today is a victory over the status quo. By adhering to OOP principles, you build a foundation that can withstand the changing needs of the business.











