In the landscape of modern software architecture, few principles hold as much weight as encapsulation within Object-Oriented Analysis and Design (OOAD). While often introduced as a method for organizing code, its true power lies in its ability to serve as a foundational layer for data security. When developers implement objects correctly, they create boundaries that protect sensitive information from unauthorized access and corruption. This guide explores the mechanics, benefits, and implementation strategies of encapsulation, focusing specifically on its contribution to maintaining robust security postures.
Security is not merely an add-on feature; it is an architectural requirement. By understanding how to bundle data and methods together, teams can reduce the attack surface of their applications. This document provides a deep dive into how information hiding works, why it matters for security, and how to apply these concepts without sacrificing maintainability. We will examine the technical nuances that separate secure design from vulnerable code structures.
Defining Encapsulation in the OOAD Context 🔍
Encapsulation is the mechanism that binds data and the methods that manipulate that data into a single unit, typically an object. In Object-Oriented Analysis and Design, this principle ensures that the internal state of an object is hidden from the outside world. The only way to interact with this state is through well-defined interfaces, often referred to as public methods or API endpoints.
This concept is rooted in the principle of information hiding. It dictates that the internal representation of an object should be independent of the code that uses it. By restricting direct access to object properties, the system enforces rules on how that data can be modified. This creates a controlled environment where data integrity is preserved.
- Encapsulation bundles data (attributes) and behavior (methods) together.
- Information Hiding restricts access to internal details.
- Interface defines the public contract for interaction.
- State Management ensures data remains valid during operations.
Without encapsulation, data becomes a free-for-all. Any part of the system can read or write to memory locations directly. This leads to unpredictable behavior, data corruption, and significant security vulnerabilities. Encapsulation acts as the gatekeeper, ensuring that every interaction goes through a verification process.
Security Implications of Information Hiding 🚫
The primary security benefit of encapsulation is the reduction of the attack surface. When data is exposed directly, malicious actors or buggy code can exploit these pathways to inject invalid data or steal sensitive information. By wrapping data within an object and exposing only specific methods, the system limits the points of entry.
Consider a scenario where a user account object holds sensitive fields like passwords or credit card numbers. If these fields are public, any code that holds a reference to the object can modify them. This is a critical failure in security architecture. Encapsulation forces developers to use methods designed to handle these fields safely.
Key security advantages include:
- Prevention of Unauthorized Modification: Direct assignment is blocked.
- Validation Enforcement: Input can be checked before state changes occur.
- Reduced Side Effects: Changes are isolated within the object.
- Auditability: All state changes pass through known methods.
This control is essential for compliance with data protection standards. Many regulations require that sensitive data be handled with strict controls. Encapsulation provides the structural means to enforce these controls at the code level, rather than relying solely on external security layers.
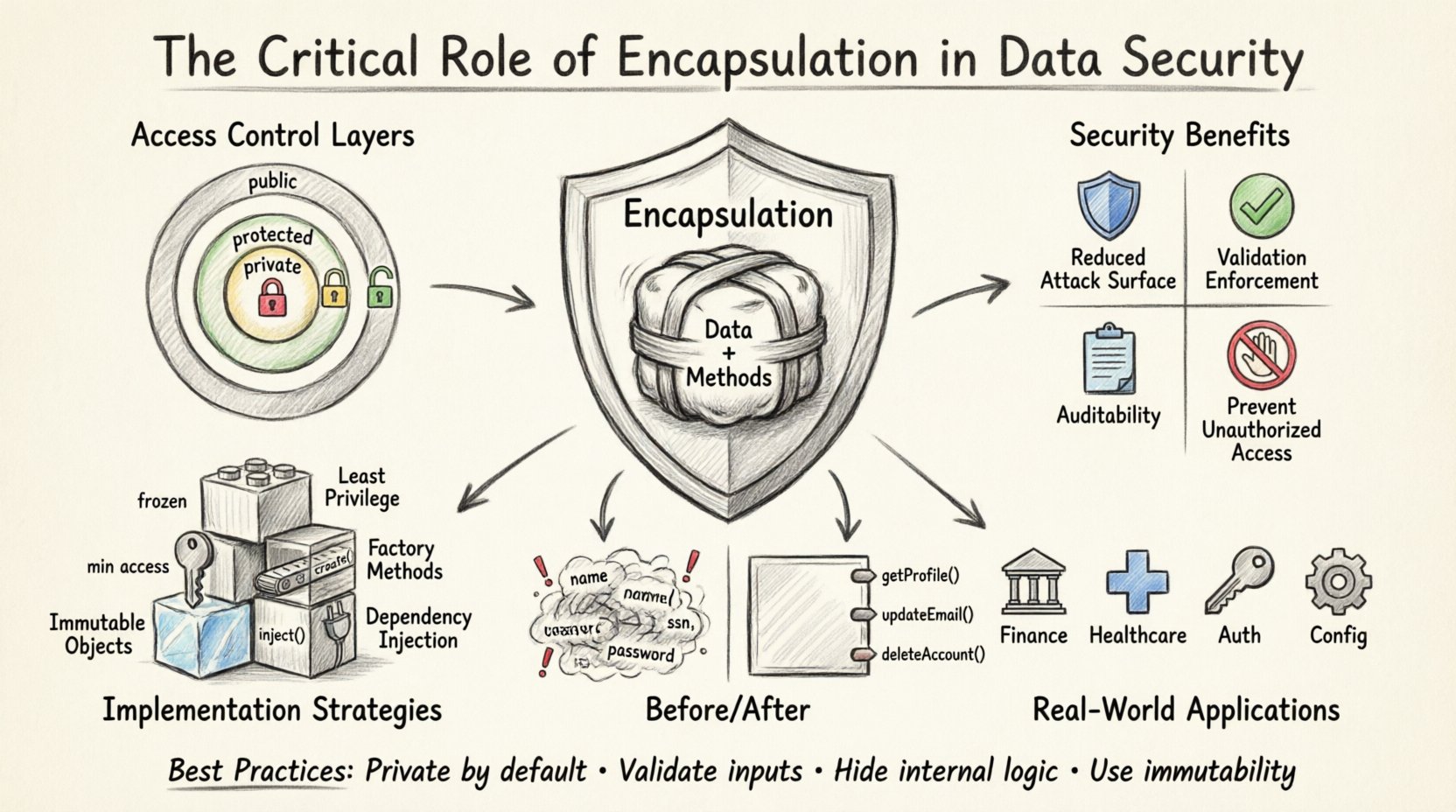
Access Control Mechanisms 🔐
Object-Oriented languages provide specific keywords to define the visibility of class members. These access modifiers are the tools used to implement encapsulation. Understanding how each modifier functions is vital for securing data.
| Modifier | Visibility | Security Use Case |
|---|---|---|
| Private | Accessible only within the class | Storing sensitive credentials or internal state. |
| Protected | Accessible within the class and subclasses | Allowing controlled inheritance without full exposure. |
| Public | Accessible from any class | Exposing safe interfaces for interaction. |
| Internal/Package | Accessible only within the same module | Limiting scope to trusted components. |
Using private modifiers is the most effective way to secure data. When a field is private, external code cannot read or write to it directly. This forces the use of public methods, such as getters and setters, which can include logic to validate inputs.
For example, a method designed to update a balance should not simply assign a new value. It must check if the transaction is valid, if the account has sufficient funds, and if the user has permission. This logic lives inside the object, protected by encapsulation.
Validating State Changes ✅
One of the most powerful aspects of encapsulation is the ability to validate data before it is stored. When a developer exposes a public method to modify an object, they can include business rules and security checks within that method. This ensures that the object never enters an invalid or insecure state.
This validation process is often referred to as input sanitization or constraint checking. It prevents common vulnerabilities such as buffer overflows, injection attacks, or logic errors that could lead to security breaches.
Strategies for validation within encapsulated objects include:
- Range Checks: Ensuring numbers fall within acceptable limits.
- Type Verification: Confirming data matches expected formats.
- State Transitions: Preventing illegal state changes (e.g., deleting a paid order).
- Null Checks: Avoiding null reference exceptions that could crash the system.
By moving validation logic into the object itself, the system becomes more resilient. If a vulnerability is found in a validation rule, it can be patched in one location, rather than hunting down every instance where the data was used.
Security Risks of Poor Encapsulation ⚠️
When encapsulation is ignored or implemented incorrectly, severe security risks arise. Developers might be tempted to expose fields directly for convenience or ease of testing. While this speeds up initial development, it creates technical debt that manifests as security flaws over time.
Common risks associated with poor encapsulation include:
- Data Leakage: Sensitive information is accessible to unauthorized modules.
- State Corruption: Invalid data overwrites valid data, causing system instability.
- Tight Coupling: Changes in one part of the system break other parts unpredictably.
- Debugging Difficulty: Tracing the source of a security breach becomes nearly impossible.
For instance, if a configuration object holds encryption keys, making those keys public allows any code to read them. This compromises the entire encryption strategy. Encapsulation ensures that keys are loaded once and used internally, never exposed to the caller.
Encapsulation vs. Abstraction 🔄
It is important to distinguish between encapsulation and abstraction, as they are often confused. Abstraction focuses on hiding complex implementation details and showing only essential features. Encapsulation focuses on bundling data and methods and restricting access to that data.
While abstraction provides a simplified interface, encapsulation provides the security boundary. A secure system requires both. Abstraction defines what the object does, while encapsulation defines how the object protects what it knows.
In practice, abstraction allows you to use an object without knowing how it works. Encapsulation ensures that the way it works cannot be tampered with. Both are necessary for a secure architecture, but encapsulation is the gatekeeper for data integrity.
Implementation Strategies for Secure Design 📝
To achieve high levels of security through encapsulation, teams should adopt specific design patterns and practices. These strategies help maintain the integrity of the system while allowing for necessary functionality.
Immutable Objects
Creating objects that cannot be changed after creation is a powerful security technique. Immutable objects eliminate the risk of state being modified unexpectedly. This is particularly useful for configuration data, user profiles, or transaction records. Once an object is created, it remains constant, ensuring that historical data is never altered.
Principle of Least Privilege
Encapsulation aligns well with the principle of least privilege. Objects should only expose the methods they absolutely need to function. If a method is not required by the external world, it should be private. This minimizes the surface area available for exploitation.
Factory Methods
Instead of allowing direct instantiation of objects with sensitive data, use factory methods. These methods control the creation process and can enforce security checks before an object is returned. This ensures that only valid, secure instances exist in memory.
Dependency Injection
Injecting dependencies through constructors rather than exposing them as public fields allows for better control. It ensures that objects are created with the correct resources and that those resources cannot be swapped out by external code.
Real-World Scenarios and Applications 🌐
Encapsulation is applied across various domains where security is paramount. Understanding these scenarios helps clarify why the principle is non-negotiable.
- Financial Systems: Account balances must never be modified directly. All changes must go through transaction methods that log the activity and verify funds.
- Healthcare Records: Patient data requires strict access controls. Encapsulation ensures that only authorized personnel can view or edit specific fields.
- Authentication Tokens: Security tokens should be stored as private strings. They should be passed through methods that handle expiration and renewal automatically.
- Configuration Management: System settings should be read-only after initialization to prevent runtime tampering.
In each of these cases, the goal is the same: prevent unauthorized or accidental modification of critical data. Encapsulation provides the structural mechanism to enforce this without relying on external permissions alone.
Performance Considerations ⚡
Sometimes developers worry that encapsulation adds overhead. While there is a minor cost to method calls versus direct field access, modern compilers optimize this significantly. The security benefits far outweigh the negligible performance difference.
Furthermore, encapsulation can improve performance by allowing better caching and optimization within the object. When data is hidden, the object can manage its own internal memory layout more efficiently without worrying about external interference.
Testing and Encapsulation 🧪
One challenge with encapsulation is testing. If data is private, unit tests cannot access it directly. This requires exposing test-specific accessors or using reflection, which can weaken security if not managed carefully.
Best practices for testing encapsulated objects include:
- Testing Behavior: Focus on what the object does, not what it contains.
- Integration Tests: Verify that the public interface works as expected in a full context.
- Mocking: Use mocks to isolate the object and test its logic without accessing internal state.
By testing the behavior, you ensure that the security logic holds up without needing to peek inside the black box. This maintains the integrity of the encapsulation during the development process.
Evolution of Security Standards 🔒
As security threats evolve, so do the standards for software design. Modern frameworks often enforce encapsulation through strict type systems and module boundaries. This shift reflects a broader industry move towards building secure systems by default.
Developers must stay updated on these changes. Ignoring encapsulation principles in favor of quick fixes can lead to vulnerabilities that are difficult to patch later. The cost of refactoring a system to add security is much higher than building it securely from the start.
Summary of Best Practices 📋
To maximize security through encapsulation, adhere to the following guidelines:
- Make all data fields private by default.
- Use public methods to expose functionality only.
- Validate all inputs within setter methods.
- Keep internal logic hidden from external callers.
- Use immutable objects where possible.
- Audit access controls regularly.
- Document the security contract of each object.
Following these practices creates a robust defense-in-depth strategy. It ensures that data is protected at the most granular level of the codebase. This approach reduces reliance on network security or external firewalls, placing the responsibility of data safety directly within the application logic.
Final Thoughts on Design Integrity 🏗️
Encapsulation is more than a coding convention; it is a design philosophy that prioritizes safety and stability. By respecting the boundaries of objects, developers create systems that are harder to break and easier to secure. This principle underpins the reliability of modern software infrastructure.
As you design your next system, consider the security implications of every class you create. Ask whether the data is protected, whether the methods enforce rules, and whether the interface is safe for public use. These questions drive the creation of secure, maintainable, and resilient software.
The integration of encapsulation into your workflow is a commitment to quality. It requires discipline and foresight, but the result is a system that stands firm against the complexities of the digital environment. Security is built into the foundation, not painted on the surface.
Adopting these principles ensures that your data remains secure, your logic remains valid, and your users remain trusting. Encapsulation is the silent guardian of your application’s integrity.











